Varlock - AI-safe .env files
 AI-safe .env files:
AI-safe .env files:
Schemas for agents, secrets for humans

Schemas for agents, secrets for humans
# Declarative schema — AI agents get full context, never secret values# @sensitive @required @type=string(startsWith=sk-ant-api)# @docs(https://platform.claude.com/docs/en/api/overview)ANTHROPIC_API_KEY=
# @type=enum(development, preview, production, test)APP_ENV=development # set non-sensitive default values directly
# use function calls and plugins to securely fetch data from external sourcesXYZ_TOKEN=op("op://api-prod/xyz/auth-token")Unlike .env.example, your .env.schema is a single source of truth, built for collaboration, that will never be out of sync. Agents can read your schema for full context — without accessing your secrets.
# built-in encryption for local overrides - NOTHING in plaintextANTHROPIC_API_KEY=varlock(local:ABC123...) Claude Code
Claude Code  CoPilot
CoPilot  Cursor
Cursor  Gemini CLI
Gemini CLI  Opencode
Opencode  Bun
Bun  Go
Go  JS/Node.js
JS/Node.js  Other languages
Other languages  PHP
PHP  Python
Python  Ruby
Ruby  TypeScript
TypeScript  Astro
Astro  Expo / React Native
Expo / React Native  Next.js
Next.js  Qwik
Qwik  React Router
React Router  SvelteKit
SvelteKit  TanStack Start
TanStack Start  Vite
Vite  1Password
1Password  Akeyless
Akeyless  AWS SSM/SM
AWS SSM/SM  Azure Key Vault
Azure Key Vault  Bitwarden
Bitwarden  Dashlane
Dashlane  Doppler
Doppler  GCP Secret Manager
GCP Secret Manager  HashiCorp Vault
HashiCorp Vault  Infisical
Infisical  KeePass
KeePass  Keeper
Keeper  macOS Keychain
macOS Keychain  Pass
Pass  Passbolt
Passbolt  Proton Pass
Proton Pass  Cloudflare Workers
Cloudflare Workers  direnv
direnv  Docker
Docker  Fly.io
Fly.io  GCP Cloud Run
GCP Cloud Run  GitHub Actions
GitHub Actions  GitLab CI
GitLab CI  Netlify
Netlify  Vercel
Vercel  AI-Safe Config
AI-Safe Config
Your .env.schema is readable by AI agents — they get full
context on your config without ever seeing secret values. Prevent leaks
to AI servers by design.
 Leak Scanning
Leak Scanning
Proactively scan your codebase for leaked secrets with varlock scan. Set up git hooks to catch leaks before they're committed.
 Runtime Protection
Runtime Protection
Redact sensitive values from logs and console output. Detect leaks in bundled client code and outgoing server responses at runtime.
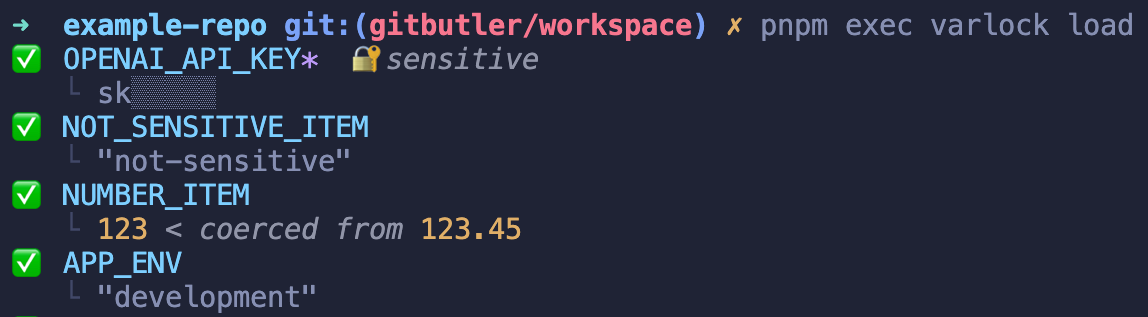
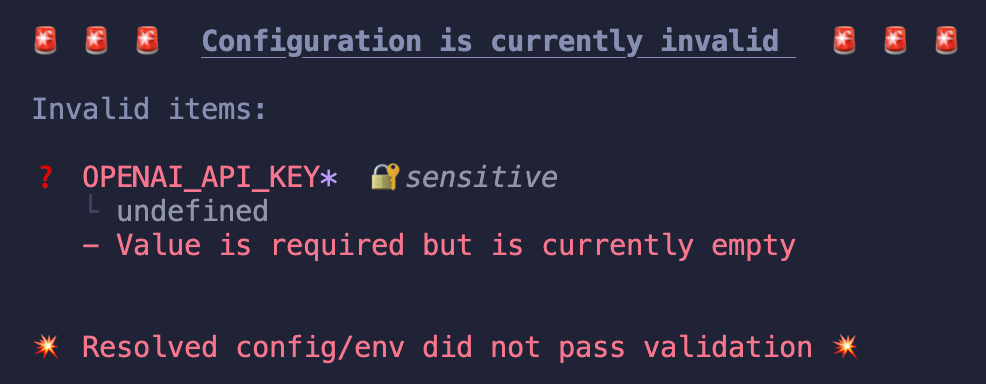
 Validation
Validation
Powerful validation capabilities, without custom logic. Misconfiguration errors are surfaced much earlier in your development cycle, with clear error messages.
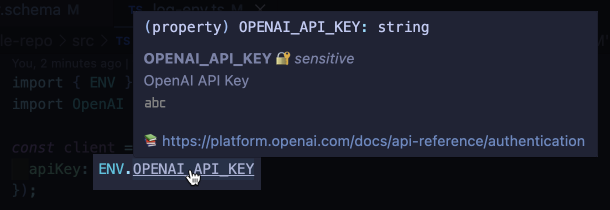
 Type-safety
Type-safety
Automatically generate types according to your schema - the single source of truth - instead of writing them by hand.
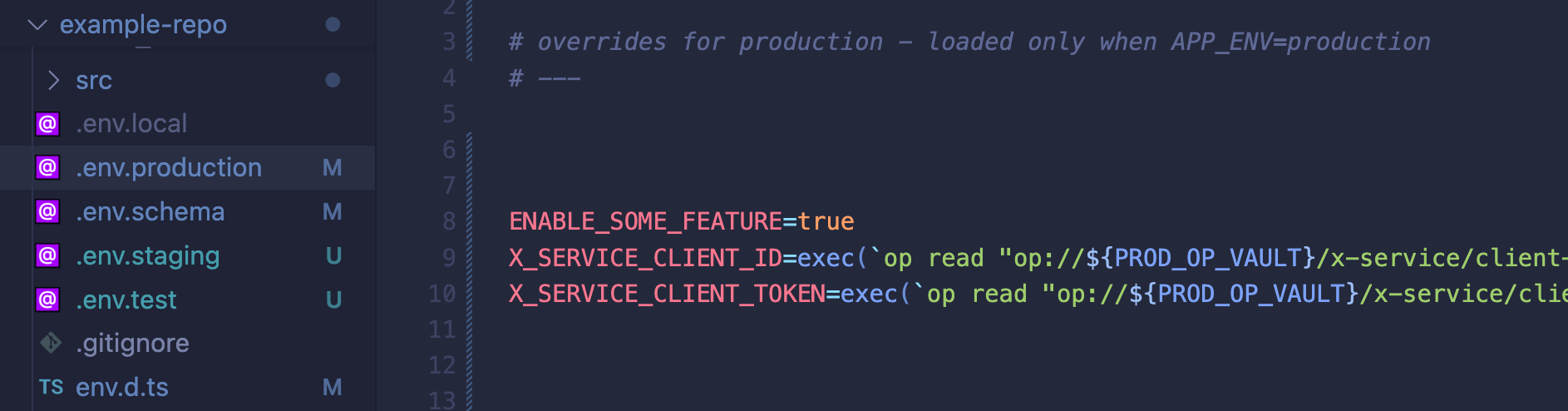
 Environments
Environments
Combine defaults, environment-specific .env files, local git-ignored overrides, and process env vars. Compose values together using functions.
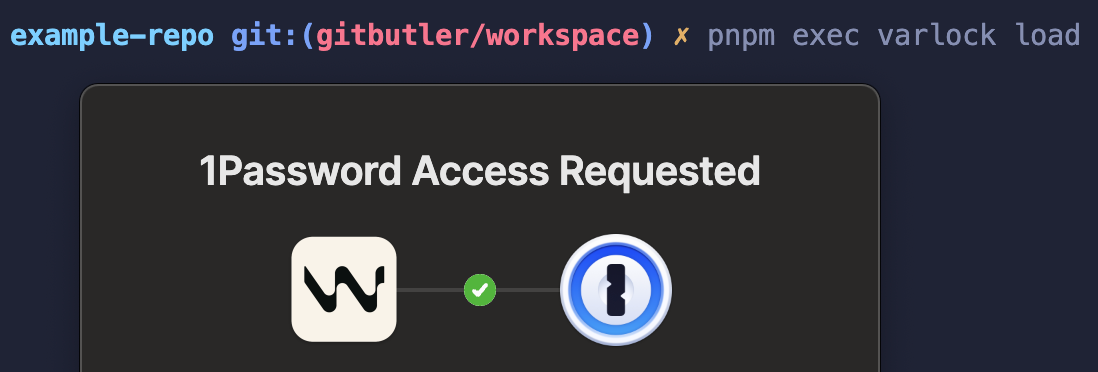
 Secure secrets
Secure secrets
Load secrets from 6 provider plugins — 1Password, Infisical, AWS Secrets Manager, Azure Key Vault, Google Secret Manager, and Bitwarden — or any CLI tool.
 Installation
Installation
# Install as a dependency in a js projectnpx varlock init
# OR install as standalone binary via homebrewbrew install dmno-dev/tap/varlock# OR via cURLcurl -sSfL https://varlock.dev/install.sh | sh -s  Drop-in replacement for dotenv
Drop-in replacement for dotenv
import 'dotenv/config'; import 'varlock/auto-load';
// *optional* type-safe env access import { ENV } from 'varlock/env'; const client = new AbcApi(process.env.ABC_API_KEY); const client = new AbcApi(ENV.ABC_API_KEY); varlock can be used as a direct replacement for dotenv in most projects. Just swap your import and get validation, security, and
more. No other code changes required!
 Run anywhere - with any language
Run anywhere - with any language
varlock run -- python my_script.py
Use varlock run to inject resolved, validated env vars into another
process.
